Last quarter, a CISO told me something that stuck with me: “We spent ₹8 crore on our IAM stack last year. This year, we’re spending ₹12 crore. And we’re less secure than we were two years ago.”
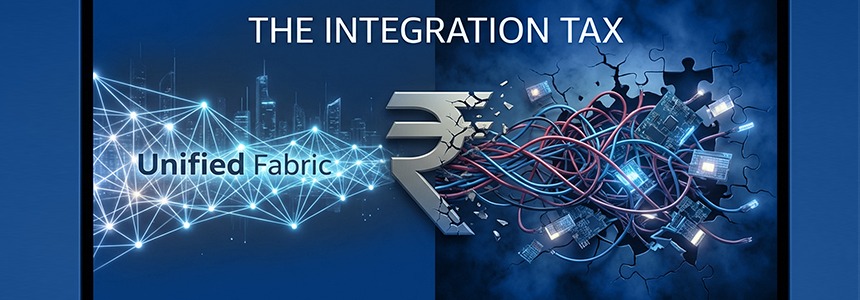
This isn’t an outlier. It’s the reality of what I call the Integration Tax—the hidden, compounding cost of stitched-together identity solutions that silently drains enterprise budgets while creating the very security gaps they’re meant to prevent.
The Invoice You Never See
When you evaluate an IAM solution, you see the license cost. What you don’t see:
The Integration Army: Three full-time engineers maintaining connectors between your SSO, PAM, IGA, and CIEM tools. Annual cost: ₹1.2-1.8 crore in salary alone.
The Consultant Carousel: External specialists hired every quarter because nobody internally understands how all the pieces fit together. Average spend: ₹40-60 lakh annually.
The Latency Tax: Every access decision traversing multiple systems adds 200-500ms. Multiply that across millions of daily requests. Your users wait. Your business slows down. Your productivity bleeds.
The Silent Security Gaps: That 15-minute window between when User A is deactivated in System 1 but still active in Systems 2, 3, and 4? That’s not a technical delay. That’s an attack window.
A recent study found that enterprises running best-of-breed IAM stacks spend 40-60% of their total IAM budget on integration and maintenance—not on actual security capabilities.
The Math That Doesn’t Add Up
Here’s the logic that gets organizations into trouble:
“Best-of-breed means we choose the best SSO solution, the best PAM solution, the best IGA solution, and integrate them. Best + Best + Best = Best overall security.”
Except it doesn’t work that way.
Best + Best + Best = Integration Hell
Because those “best” solutions were each designed to be the center of your identity universe. None were designed to be a cooperative piece in someone else’s puzzle.
The result? You don’t get 3 excellent solutions working in harmony. You get 3 excellent solutions working against each other, held together by custom code that breaks every time one vendor releases an update.
One global financial services firm calculated their true IAM cost: ₹18 crore in licenses, ₹24 crore in integration and maintenance. They were spending 133% more on making their tools talk to each other than on the tools themselves.
The Hidden Costs Nobody Talks About
1. The Blame Game Tax
When something breaks (and it will), who’s responsible? Your SSO vendor blames the PAM vendor. The PAM vendor blames the IGA vendor. The IGA vendor blames the network. Meanwhile, your security team spends 40 hours troubleshooting instead of securing.
Real cost: 15-20% of security team time spent on vendor coordination, not security work.
2. The Innovation Lag
That new AI-powered risk engine your IGA vendor released? It can’t talk to your PAM system without custom development. That Zero Trust feature from your SSO provider? Requires reconfiguring 15 integrations.
By the time you implement innovations, they’re no longer innovative.
Real cost: 6-18 month lag on adopting new capabilities your competitors deploy in weeks.
3. The Talent Trap
You can’t hire one IAM expert anymore. You need an SSO specialist, a PAM specialist, an IGA specialist, and someone who understands how they all integrate. Finding that team? Good luck.
Real cost: 30-40% higher salary premiums for multi-tool IAM specialists, when you can find them.
4. The Downtime Multiplier
One component fails? In a stitched environment, the blast radius is unpredictable. Your SSO goes down and suddenly nobody can access anything—even systems that shouldn’t be affected.
Real cost: Average 3x longer mean time to recovery compared to unified platforms.
Enter Cybersecurity-as-an-Infrastructure (CSaaI)
There’s a different approach: treating identity security as foundational infrastructure, not as a collection of tools.
This is what we call CSaaI—Cybersecurity-as-an-Infrastructure.
Instead of stitching together multiple products, you deploy a unified fabric where access management, identity governance, privileged access, and risk intelligence exist as a single, cohesive layer.
The difference is architectural:
Stitched Stack Approach: Five different databases, seven API integrations, custom code holding it together, multiple admin consoles, overlapping audit logs.
Unified Fabric Approach: Single codebase, shared context across all identity decisions, one source of truth, unified governance, deterministic outcomes.
The Business Case: Real Numbers
Let’s look at what happens when you eliminate the Integration Tax:
Scenario: Mid-size enterprise, 5,000 employees, multi-cloud environment
Traditional Best-of-Breed Stack:
- Licenses: ₹1.2 crore/year
- Integration development: ₹80 lakh
- Ongoing maintenance: ₹1.1 crore/year
- Consultant fees: ₹50 lakh/year
- Internal team overhead (40% time on integration): ₹90 lakh/year
- Total 3-year cost: ₹13.8 crore
Unified CSaaI Platform:
- Platform license: ₹1.5 crore/year
- Implementation: ₹40 lakh (one-time)
- Ongoing maintenance: ₹20 lakh/year
- Internal team overhead (10% time): ₹25 lakh/year
- Total 3-year cost: ₹5.8 crore
Savings: ₹8 crore over 3 years—a 58% reduction in total cost of ownership.
And this doesn’t account for:
- Faster incident response (40-60% improvement)
- Reduced security gaps (90%+ reduction in blind spots)
- Accelerated compliance audits (75% time reduction)
- Better security posture (measurably fewer vulnerabilities)
What Integration Tax Actually Buys You
Here’s the uncomfortable truth: Integration Tax doesn’t buy you better security. It buys you:
❌ Complexity that slows down your team
❌ Vulnerabilities in the seams between systems
❌ Delayed response to threats
❌ Audit nightmares
❌ Vendor finger-pointing
❌ Inability to adapt quickly
The Questions Finance Should Be Asking
If you’re a CFO or finance leader reviewing IAM budgets, here are the questions that matter:
- What percentage of our IAM budget goes to making tools work together vs. actual security?
- How many FTEs are dedicated to integration and maintenance?
- What’s our mean time to implement new security capabilities?
- How many vendors do we need to coordinate during a security incident?
- What’s the total loaded cost per identity, including all hidden costs?
If these questions aren’t being asked, you’re likely paying the Integration Tax without realizing it.
The Path Forward
The shift from stitched stacks to unified infrastructure isn’t just technical—it’s strategic.
Organizations making this shift report:
- 60-70% reduction in total IAM operational costs
- 10x faster deployment of new capabilities
- 3-5x improvement in mean time to respond to threats
- 90% reduction in security team time spent on tool coordination
Your identity stack shouldn’t require an army of integrators. True security infrastructure pays for itself through operational efficiency.
The Bottom Line
Every rupee spent on Integration Tax is a rupee not spent on actual security. Every hour your team spends troubleshooting integrations is an hour they’re not detecting threats. Every delay in implementing new capabilities is a window your competitors are exploiting.
The question isn’t whether you can afford to move to a unified architecture.
It’s whether you can afford not to.