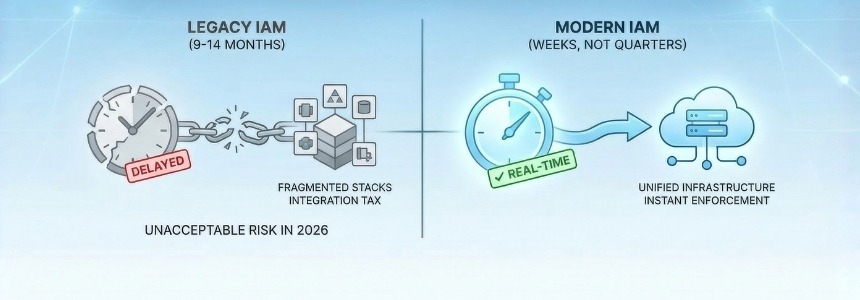
In the time it takes to implement a legacy Identity and Access Management (IAM) suite, an autonomous AI agent can initiate and complete thousands of cross-border transactions. A sophisticated hacker can move laterally through a multi-cloud environment ten thousand times over. A global regulation can be drafted, debated, passed, and enforced.
Yet, for some reason, the enterprise world still accepts an industry “standard” for IAM deployment that ranges from 9 to 14 months.
The problem is that identity is no longer just about employees and contractors. Non-human identities now outnumber human identities 82:1 in the average enterprise. In cloud-native environments, that ratio can reach 40,000:1. And 99% of service accounts are over-permissioned (Gartner IAM Summit 2025).
In a world where machines operate at machine speed, waiting nine months to govern identity isn’t just slow, it’s dangerous.
In 2026, nine months isn’t just a project timeline, it’s an eternity of exposure.
It’s time we pull back the curtain on why these projects take so long and establish a new benchmark for the modern era: The 9-Week Promise.
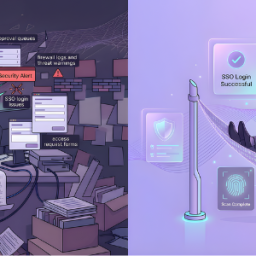
The “Integration Tax”: The Hidden Cost of Fragmented Security
The legacy giants of the IAM world are almost universally a patchwork of acquisitions. They offer a Governance tool from one era, a Privileged Access vault from another, and a Cloud Identity module bolted on more recently. Even when sold under a single, shiny brand name, these products exist as disparate codebases with different DNA.
When you buy them, you aren’t actually buying a finished product; you are buying a massive, expensive construction project. You spend the first six months of your timeline paying an army of professional services consultants to build fragile API bridges between these modules just to get them to share a basic user list.
This is what we call the “Integration Tax.” It is the hidden tax on your time, your budget, and your security. While your team is busy “stitching” data schemas together, your “Shadow Admins” in your cloud environment remain unmonitored and your offboarding processes remain dangerously manual.
The Trap of “Identity Latency”
The problem with a “stitched-together” stack isn’t just the time it takes to build; it’s how it behaves once it’s finally live. Because these tools are connected by APIs rather than a shared heart, they suffer from what we call Identity Latency.
Consider the “Offboarding Lag.” In a legacy environment, you disable a user in your HR system. That signal travels to your Governance tool, which then has to “sync” that status to your Privileged Vault. If that sync happens every hour, or even every fifteen minutes, you have a window of opportunity for a disgruntled employee or an external attacker to do irreparable damage.
In the era of machine-speed attacks, a fifteen-minute window is a lifetime. True security requires zero-latency identity. When a user is disabled, their access across every privileged silo must vanish instantly, not eventually.
The Converged Alternative: Engineering Speed
True convergence isn’t about a pretty dashboard that pulls data from five different places. It’s about a Unified Codebase.
When Identity Governance (IGA), Privileged Access (PAM), and Cloud Security (CIEM) share a single data schema and a single heart, the “Integration Phase” of your project simply disappears. There are no APIs to write, no databases to synchronize, and no “Integration Tax” to pay.
By moving to a converged codebase, we’ve realized that the 9-month project isn’t a technical necessity, it’s a byproduct of bad architecture. When the tools are natively unified, the implementation becomes about configuration, not custom coding. You aren’t building the engine; you’re just turning the key.
The 9-Week Promise: Setting a New Standard
We are challenging the industry to move from marathons to sprints. We believe that a modern enterprise should be able to move from “Identity Chaos” to “Identity Certainty” in months, not years.
This is the new 2026 benchmark:
- Weeks 1–2: Foundation. Infrastructure setup and initial identity ingestion.
- Weeks 3–5: Gap Closure. Policy normalization and closing the critical holes in privileged access.
- Weeks 6–9: Validation. User Acceptance Testing, audit-ready reporting, and full Go-Live.
A Call to Action for IT Directors
It is time to stop accepting “complexity” as a valid excuse for implementation bloat. Every month your IAM project sits in “Integration Hell” is a month your organization is paying for security it doesn’t actually have. It’s a month where you are failing to meet the expectations of your board and your auditors.
Demand more from your vendors. Ask the hard questions:
- “Do your IGA and PAM modules share a single database, or are they just integrated via API?”
- “Can you show me a path to full production value in less than three months?”
- “Am I paying for a solution, or am I paying for a construction project?”
- If your 2026 IAM project is a marathon, you aren’t building a defense, you’re building legacy debt. It’s time to switch to a sprint.
Is your team currently paying the “Integration Tax”? Let’s discuss in the comments how we can move toward a 9-week standard.
Source: Click Here