Executive Summary
The average CISO tenure of 18-24 months isn’t a career milestone—it’s a systemic failure. CISOs face impossible expectations: prevent all breaches without slowing business, with insufficient budgets, while bearing personal liability for outcomes. They operate under a brutal blame equation where 10,000 prevented incidents earn no recognition, but one breach threatens their career. Many report to CIOs (creating inherent conflict), lack resources despite accountability, and work in isolation with nowhere to process crushing stress. This isn’t individual weakness—it’s structural dysfunction that’s making organizations less secure. The solution requires fundamental change: structural independence, realistic expectations, adequate resources, shared accountability, and organizational culture that treats security as everyone’s responsibility, not just the CISO’s burden. Read on to understand why security leadership is burning out and what must change.
The average tenure of a CISO is 18-24 months. That’s not a career milestone—it’s a warning sign.
Yet in boardrooms and at security conferences, we don’t talk about why CISOs are burning out faster than any other C-suite role. We don’t discuss the impossible expectations, the blame culture, or the crushing weight of trying to secure organizations that fundamentally don’t want to be inconvenienced by security.
Instead, we celebrate the next CISO hire and pretend the revolving door is normal.
It’s not normal. It’s a crisis. And it’s making organizations less secure.
The Impossible Job Description
Let’s be honest about what we’re asking CISOs to do:
Prevent all breaches (impossible) Without slowing down the business (contradictory) With insufficient budget (guaranteed) While managing complex compliance requirements (soul-crushing) And taking personal liability when things go wrong (career-ending)
Oh, and do it all with:
- Legacy systems you can’t replace
- Shadow IT you can’t control
- Executives who demand security exceptions
- Users who despise security friction
- Attackers who are better funded than you
- A board that doesn’t understand the threat landscape
- Vendors who oversell and underdeliver
This isn’t a job description. It’s a setup for failure.
The Blame Equation
Here’s the unspoken CISO accountability model:
If there’s no breach: “What exactly are we paying you for? Nothing happened.”
If there’s a breach: “Why didn’t your security program prevent this? What were we paying you for?”
CISOs are blamed for breaches but get no credit for preventing them. Every day without an incident is invisible success. Every incident is visible failure—regardless of the context, constraints, or warnings that were ignored.
The math is brutal:
- 10,000 threats blocked = “just doing your job”
- 1 threat that gets through = “security failure”
No other C-suite role operates under this equation. CFOs aren’t fired when quarterly revenue misses projections by 0.1%. COOs aren’t personally liable when a shipment is delayed.
But CISOs? One breach and their career is in question.
The “Security Versus Business” False Dichotomy
CISOs are constantly told to “balance security with business needs”—as if security isn’t a business need.
Here’s what that actually means in practice:
Business unit: “We need this cloud application deployed by Friday.” CISO: “We need to assess vendors, review security controls, and configure proper access governance. That takes 2-3 weeks.” Business unit: “So you’re saying security is blocking business innovation?”
Sales: “This deal requires us to share customer data with the partner.” CISO: “That violates our data protection policy and regulatory requirements.” Sales: “So you’re saying you don’t care about revenue?”
CEO: “We need to move faster. Stop making people jump through security hoops.” CISO: “Those controls prevent breaches that could destroy the company.” CEO: “Why is security so negative? Be a business enabler, not a blocker.”
CISOs are asked to enable the business—right up until there’s a breach. Then they’re asked why they enabled risky behavior.
The Reporting Structure Problem
Many CISOs report to the CIO. Think about that:
The person responsible for security reports to the person responsible for keeping systems running and delivering projects on time.
Guess whose priorities win when there’s a conflict?
When the CISO says “we need to patch this critical vulnerability,” and the CIO says “that system can’t go down during business hours,” who prevails?
When the CISO says “we need to delay this application launch for security review,” and the CIO’s performance metrics depend on on-time delivery, what happens?
Even well-intentioned CIOs face an impossible conflict of interest. Security requires saying “slow down, think about risk, add controls.” Operations requires “ship faster, reduce friction, maintain availability.”
CISOs who report to CIOs are structurally positioned to lose.
The Budget Theater
Every year, CISOs go through budget negotiations:
CISO: “We need $2M for security program improvements.” CFO: “What’s the ROI?” CISO: “Reduced breach probability and impact.” CFO: “Can you quantify that?” CISO: “Breach cost is estimated at $4M-$50M depending on scope.” CFO: “So you’re asking for $2M to prevent something that might not happen?” CISO: “That’s literally what security is.” CFO: “Approved for $500K. Make it work.”
Then a breach happens.
Board: “Why didn’t we have adequate security controls?” CISO: “We requested budget for those controls. It was denied.” Board: “That’s not an acceptable answer. Security is your responsibility.”
CISOs are held accountable for security outcomes but aren’t given authority over the resources required to achieve them.
The Vendor Fatigue
CISOs are drowning in vendor pitches. Every week brings:
- 47 meeting requests from security vendors
- 23 “urgent” product demos
- 15 analyst reports about emerging threats
- 8 invitations to security conferences
- Dozens of LinkedIn messages from sales reps
Each vendor claims their tool will “solve” security. But CISOs know:
- No tool solves security
- Most tools create integration challenges
- Vendor consolidation promises rarely deliver
- Security teams are already overwhelmed managing existing tools
Yet the pressure to “stay current” means constantly evaluating new solutions while trying to make existing ones actually work.
The result: Analysis paralysis, vendor fatigue, and the nagging fear that you’re missing the one tool that could have prevented the next breach.
The Compliance Hamster Wheel
CISOs are buried in compliance requirements:
- SOC 2 audits
- ISO 27001 certification
- PCI DSS assessments
- GDPR compliance
- HIPAA requirements
- Industry-specific regulations
- Customer security questionnaires
- Vendor risk assessments
Each framework demands:
- Documentation
- Evidence collection
- Control testing
- Remediation tracking
- Regular re-certification
The problem: Compliance doesn’t equal security.
You can be fully compliant and still get breached. But non-compliance creates immediate business consequences: failed audits, lost deals, regulatory fines, customer churn.
So CISOs spend 60% of their time on compliance theater and 40% on actual security—then get blamed when the 40% isn’t enough.
The Skill Gap Crisis
CISOs are expected to be experts in:
- Technical security (infrastructure, application, cloud, endpoint)
- Risk management frameworks
- Compliance and regulatory requirements
- Vendor management
- Incident response
- Security operations
- Identity and access management
- Business strategy
- Financial planning
- Board communication
- Crisis management
- Team leadership
Oh, and stay current with:
- Emerging threats
- New attack techniques
- Evolving technology landscape
- Changing regulations
- Security tool innovations
This isn’t a job. It’s five jobs pretending to be one.
CISOs who are technical enough to architect security solutions are told they need more business acumen. CISOs who excel at business communication are told they need deeper technical expertise.
The unicorn CISO who has all these skills is either mythical or already burned out.
The Incident Response Nightmare
When a breach happens, CISOs experience:
Hour 1-4: Panic, investigation, containment Hour 4-24: All-hands response, forensics, business impact assessment Day 2-7: Remediation, recovery, stakeholder communication Week 2-4: Post-incident analysis, board reporting, regulatory notification
Then:
- Media coverage analyzing what went wrong
- Board questions about CISO competence
- Executive team blame assignment
- Legal investigations
- Regulatory inquiries
- Customer lawsuits
- Insurance claims
- Career uncertainty
All while trying to prevent the next incident.
Most CISOs live in constant low-grade fear of the 2 AM phone call that starts this cascade.
The Loneliness of the Role
CISOs operate in a unique isolation:
They can’t fully trust their team because security incidents might involve insider threats or compromised accounts.
They can’t be fully honest with executives because admitting the true extent of risk exposure would cause panic or dismissal.
They can’t share details with peers at other companies because competitive intelligence and regulatory requirements limit transparency.
They can’t vent to family because the technical details and confidentiality requirements make conversations impossible.
They can’t show weakness because security leadership requires projecting confidence even when facing overwhelming uncertainty.
The result: CISOs carry immense stress with nowhere to process it.
The Personal Toll
The burnout manifests in predictable ways:
Physical:
- Chronic stress
- Sleep deprivation (responding to incidents at all hours)
- Health problems (heart issues, high blood pressure)
- Exhaustion that no vacation can fix
Mental:
- Anxiety about inevitable breaches
- Depression from constant criticism
- Impostor syndrome (“am I qualified for this?”)
- Hypervigilance that never turns off
Relationship:
- Missed family events due to incidents
- Inability to disconnect from work
- Stress bleeding into personal relationships
- Isolation from non-security people who don’t understand
Career:
- Resume gaps after burnout-driven departures
- Reluctance to take another CISO role
- Industry exit to less stressful positions
- Early retirement from the field
This isn’t sustainable. And the industry knows it but won’t admit it.
Why Organizations Don’t Fix This
If CISO burnout is this obvious, why isn’t it addressed?
Because fixing it requires admitting uncomfortable truths:
1. Security is expensive and inconvenient Real security slows things down and costs money. Organizations want security outcomes without security investment.
2. Blame is easier than accountability Holding CISOs personally responsible is simpler than holding the entire organization accountable for security culture.
3. Executives don’t want constraints Leadership wants to be exempt from security policies. Empowering CISOs means constraining executive behavior.
4. Boards don’t understand cyber risk Most board members can’t evaluate CISO performance because they don’t understand the threat landscape or security controls.
5. The market enables dysfunction There’s always another CISO candidate willing to take the job. Why fix the role when you can just replace the person?
What Actually Needs to Change
Addressing CISO burnout requires organizational transformation, not individual resilience training:
1. Structural Independence
CISOs must report to the CEO or board, not the CIO. Security cannot be effective when subordinate to operational priorities.
2. Realistic Expectations
Stop expecting CISOs to prevent all breaches. Start measuring them on:
- Risk reduction
- Incident response effectiveness
- Security program maturity
- Team development
- Business enablement
3. Adequate Resources
If you’re not willing to fund security properly, don’t hold CISOs accountable for security outcomes. Match responsibility with authority and resources.
4. Shared Accountability
Security is everyone’s job. Business units, development teams, executives—all must be held accountable for security, not just the CISO.
5. Psychological Support
CISOs need:
- Peer support networks
- Executive coaching
- Mental health resources
- Reasonable work-life boundaries
- Protection from personal liability for organizational risk decisions
6. Board Education
Boards must understand:
- What CISOs can realistically achieve
- What security success looks like
- How to evaluate security programs
- Why blame culture drives talent away
7. Culture Change
Stop treating security as “the CISO’s problem.” Security is a business capability that requires organization-wide commitment.
The Conversation We Need to Have
If you’re on a board or in executive leadership, ask yourself:
Are we setting our CISO up for success or failure?
Do they have:
- Adequate budget and resources?
- Authority to enforce security policies?
- Support when they slow down business initiatives for security reasons?
- Realistic expectations about what security can achieve?
- Protection from personal liability for organizational risk decisions?
If not, you’re not hiring a CISO. You’re hiring a scapegoat.
If you’re a CISO, ask yourself:
Is this role sustainable? Am I:
- Constantly fighting for basic resources?
- Blamed for risks I warned about but couldn’t get funding to address?
- Working unsustainable hours to meet impossible expectations?
- Experiencing physical or mental health impacts?
- Questioning whether this is worth it?
If so, the problem isn’t you. It’s the system.
The Bottom Line
The CISO burnout crisis isn’t a personal weakness issue. It’s a structural dysfunction issue.
We’ve created a role with impossible expectations, insufficient authority, inadequate resources, and crushing personal liability. Then we wonder why people burn out and leave.
The 18-24 month average tenure isn’t a reflection of CISO capability. It’s a reflection of organizational failure to create sustainable security leadership roles.
Organizations that continue treating CISOs as expendable will cycle through talent while their security posture deteriorates. The institutional knowledge lost with each departure, the program disruption, the repeated rebuilding—all create the conditions for breaches.
The industry can do better. Organizations can do better. We must do better.
Because cybersecurity is too important to be left to burned-out leaders operating in dysfunctional systems.
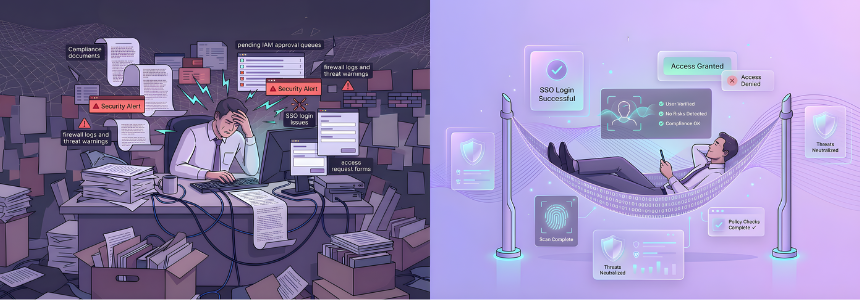
How Cross Identity nimbleNova Reduces CISO Burden and Enables Success
One of the primary sources of CISO burnout is fighting daily battles with identity management chaos—orphaned accounts, manual access reviews, compliance evidence gathering, and the constant firefighting that comes from fragmented identity infrastructure. Cross Identity’s nimbleNova platform directly addresses these operational drains that consume CISO bandwidth and prevent strategic security leadership.
nimbleNova empowers CISOs by:
Automating What Burns Teams Out: Eliminate the manual identity lifecycle processes that consume 60% of security team time. Automated provisioning, deprovisioning, access reviews, and compliance reporting free CISOs to focus on strategy instead of spreadsheets.
Providing Board-Ready Visibility: Real-time dashboards and executive reporting that translate identity risk into business terms. Finally answer “who has access to what” with confidence, turning board presentations from defensive exercises into strategic conversations.
Reducing Compliance Burden: Continuous compliance monitoring and automated evidence collection for SOC 2, ISO 27001, GDPR, and other frameworks. What used to take weeks of manual work becomes automated attestation workflows.
Enabling Risk-Based Decision Making: Context-aware access analytics and risk scoring that help CISOs prioritize what actually matters instead of drowning in alerts. Make informed decisions about where to invest limited resources.
Creating Organizational Accountability: Self-service access requests with automated approval workflows put identity governance in the hands of business units and data owners—finally distributing security responsibility beyond the CISO’s desk.
Organizations implementing nimbleNova report 65% reduction in identity-related security team workload and 80% faster compliance audit preparation—directly addressing two of the largest contributors to CISO burnout.
CISOs deserve tools that work for them, not platforms that create more work. nimbleNova was built by security practitioners who understand that sustainable security leadership requires technology that enables strategic thinking instead of tactical firefighting.
Schedule a consultation to see how nimbleNova can reduce your identity management burden and give you back the time to be the strategic security leader your organization needs—before burnout makes that decision for you.
Source: Click Here