Why modern enterprises must move beyond tool-led security
For years, cybersecurity has been treated as a tooling problem. New threats appeared, and organizations bought new products. Environments expanded, and teams added more layers.
Over time, security became a stitched stack of point solutions connected through integrations, dashboards, and manual workflows.
That approach no longer works.
Modern enterprises operate in environments where identities multiply continuously, cloud permissions shift daily, and attackers exploit gaps faster than humans can respond.
Cybersecurity can no longer behave like disconnected tools. It must behave like infrastructure: always-on, cohesive, and enforceable by design.
Tools solve functions. Infrastructure enforces outcomes.
Security tools handle specific domains: authentication, governance, privileged access, entitlements, detection. Individually, many work well. But enterprise security is not a set of independent functions. It is one operating reality where identity and access decisions must remain consistently enforced across systems, environments, and time.
Tools were never built to guarantee that consistency. Infrastructure is.
The real problem isn’t under-investment. It’s fragmentation.
Most organizations aren’t lacking security products. They’re over-fragmented. Access is managed in one system. Governance lives in another. Privileged control sits elsewhere. Risk intelligence stays trapped in dashboards disconnected from enforcement.
The result is predictable:
- Policies drift
- Exceptions accumulate
- Enforcement becomes inconsistent
- Audits get harder every quarter
This is not a failure of execution. It is a failure of architecture.
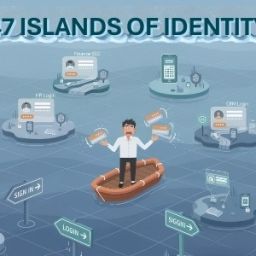
The silent threat: entitlement creep
Entitlement creep accumulates quietly, role changes add permissions, temporary access becomes permanent, cloud privileges multiply invisibly. Eventually, one compromised credential can take down your organization.
The fragmented reality
Most organizations respond with more tools: CIEM detects but can’t revoke, IGA certifies but lacks cloud visibility, PAM controls sessions but misses risky access, IRM scores risk but can’t enforce. One detects, another reviews, another controls, none act together, none enforce in real time. By the time alerts flow through batch syncs and manual workflows, the damage is done.
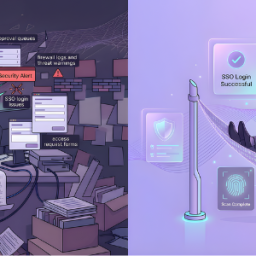
The Cross Identity Difference
We built a single Identity Fabric where CIEM, IGA, PIAM, and IRM operate as one — not separate products bolted through APIs. CIEM detects excessive permissions → IGA flags for certification → PIAM converts to just-in-time access → IRM correlates risk → Policy enforces in real time. Total elapsed time: seconds.
The bottom line
Access creep isn’t a visibility, governance, privilege, or risk problem, it’s all of them simultaneously. You can’t fix a unified problem with fragmented tools.
Cross Identity CSaaI: One platform. Complete visibility. Unified governance. Real-time enforcement.
Identity becomes the foundation of cybersecurity infrastructure.
As the perimeter disappears, identity becomes the only constant across users, workloads, APIs, applications, and cloud systems.
Every access decision is ultimately an identity decision.
That’s why Cybersecurity-as-an-Infrastructure (CSaaI) begins with identity as the control plane, where access, governance, privilege, and risk operate as one cohesive layer instead of separate products coordinating imperfectly.
Tools are purchased. Infrastructure is built.
The future of cybersecurity won’t be defined by how many tools an organization owns. It will be defined by whether security behaves like infrastructure: always-on, consistent, and enforceable at scale. Enterprises don’t need more control. They need a stronger foundation.