Executive Summary
CISOs and IT leaders struggle to communicate identity risk to boards because they speak different languages. Security teams present technical details—MFA adoption rates, privileged account counts, access review completion—while boards think in business terms: revenue impact, regulatory exposure, operational resilience. This translation gap leaves boards unaware that identity compromise is the leading breach vector. Effective board communication requires reframing identity risk in business language: quantifying breach cost exposure from identity weaknesses, connecting identity failures to regulatory penalties, demonstrating operational impact, and benchmarking identity maturity against peers. Boards understand risk when presented as financial exposure, compliance liability, and competitive disadvantage—not as technical metrics.
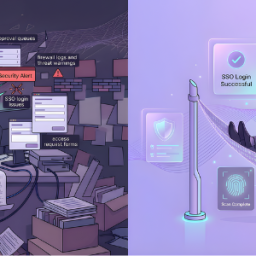
Every quarter, CISOs present security updates to boards showing metrics: MFA enrollment percentages, access review completion rates, privileged account counts. Boards nod politely and move on. Then a breach happens through compromised credentials, and the board asks: “Why didn’t you tell us this was a risk?”
The CISO did tell them. They just did not speak the same language.
The Translation Problem
Security professionals think in technical controls. Boards think in business outcomes.
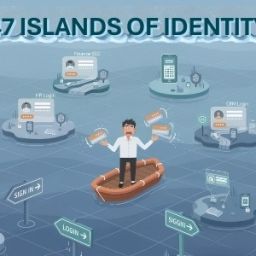
When a CISO says “we have 3,000 orphaned accounts,” the board hears words without context. They do not understand that orphaned accounts represent unauthorized access, creating breach exposure and regulatory violations.
When a CISO reports “privileged access management is 60% complete,” the board sees reasonable IT project progress. They do not grasp that 40% of privileged access remains ungoverned, allowing unauthorized changes without detection.
What Boards Actually Care About
Boards focus on three concerns: financial performance, regulatory compliance, and strategic positioning.
Identity risk matters to boards only when connected to these:
Financial Impact: Breach costs, incident response expenses, regulatory fines, customer compensation, insurance premiums
Regulatory Exposure: GDPR penalties up to 4% of global revenue, DPDPA fines up to ₹250 crore, SOC2 failures losing customers
Operational Resilience: Business continuity, customer trust, competitive positioning, ability to win regulated contracts
The Identity Risk Narrative Framework
Translate technical posture into business risk: Current State → Business Exposure → Impact → Remediation
Ineffective: “We have 2,500 accounts with standing privileged access.”
Effective: “2,500 administrator accounts maintain permanent elevated privileges. If compromised, attackers gain immediate access to production systems and customer data. Industry data shows compromised privileged accounts result in breaches averaging $4.5M. We can reduce this exposure 80% through just-in-time privilege management, requiring $200K investment over six months.”
Translating Technical Metrics
Technical: “Access review completion rate is 75%” Board Translation: “25% of employee access is unvalidated, creating compliance risk and potential access by terminated employees—direct breach exposure.”
Technical: “MFA enrollment is 85%” Board Translation: “15% of accounts remain vulnerable to credential theft—the leading breach vector. Industry data shows MFA blocks 99% of attacks. Our incomplete deployment leaves 750 accounts exposed.”
Technical: “Average provisioning time is 5 days” Board Translation: “New employees wait a week for system access, impacting productivity. Sales representatives cannot access CRM, directly affecting pipeline.”
The Risk Quantification Approach
Boards understand numbers:
“Based on current identity posture, a successful phishing attack has 60% probability of broader breach. Industry average breach cost for our size is $3.8M. Our cyber insurance covers $2M, leaving $1.8M exposure plus reputational impact.”
Use frameworks boards recognize:
- Probability × Impact = Quantified risk
- Remediation Cost vs. Risk Reduction = ROI
The Peer Benchmark Strategy
Boards are competitive. Frame identity maturity against industry:
“Our privileged access management maturity is Level 2 on a 5-point scale. Industry leaders average Level 4. This gap creates competitive disadvantage—we lost two major deals last quarter partially due to security concerns during vendor assessments.”
The Regulatory Penalty Reality
“GDPR requires appropriate access controls. Our identity governance gaps—excessive privileges, slow deprovisioning, incomplete reviews—create potential penalties up to 4% of global revenue, approximately $15M. Current identity governance investment is $500K annually. The risk-adjusted ROI is clear.”
What to Stop Doing
- Stop using unexplained acronyms
- Stop presenting metrics without business context
- Stop assuming technical knowledge
- Stop making security an IT-only topic
The Bottom Line
Boards do not understand identity risk because security leaders present it in technical language.
CISOs must become translators, converting identity security posture into business risk narratives.
When identity risk is quantified financially, connected to regulatory exposure, and benchmarked against competitors, boards understand immediately.
Your board wants to understand identity risk and make informed decisions. Give them that information in language they can act on.
How Cross Identity Provides Board-Ready Identity Visibility
Cross Identity translates complex identity posture into executive dashboards and board-ready reporting that quantifies risk in business terms—providing real-time identity risk scoring, compliance status, automated reports with quantified exposure, and peer benchmarking.
Source: Click Here