Executive Summary
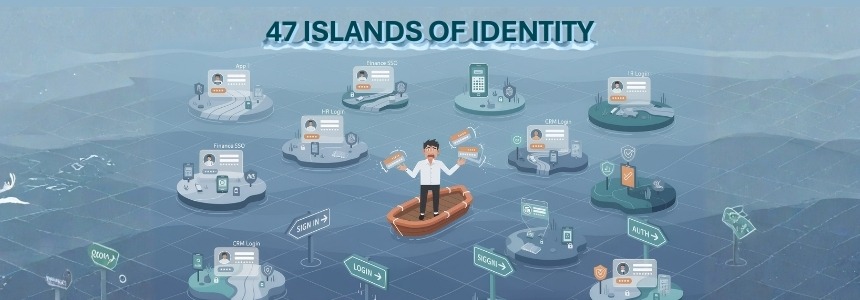
Organizations implemented Single Sign-On (SSO) expecting unified identity management and simplified access control. Instead, most enterprises now operate 47+ disconnected identity silos—each SSO instance managing its own user population, authentication methods, and access policies without coordination. This fragmentation occurred because SSO was deployed tactically (application by application) rather than strategically, legacy systems couldn’t integrate, different business units chose different SSO providers, mergers brought competing identity platforms, and nobody governed the overall identity architecture. The result: users have multiple “single” sign-ons, IT manages redundant identity infrastructure, security has no unified view of access, and the promise of simplified identity management became a nightmare of complexity. True identity consolidation requires treating identity as an enterprise capability with centralized governance, not a feature that each application implements independently. Organizations must move from “SSO everywhere” to “unified identity governance” with a single source of truth for identities, federated authentication that actually federates, and centralized policy enforcement across all access points.
You deployed Single Sign-On to simplify identity management. One login, access to everything, streamlined user experience. Problem solved.
Except now you have:
- Okta for SaaS applications
- Azure AD for Microsoft 365
- Legacy Active Directory for on-premises apps
- AWS IAM for cloud infrastructure
- Custom SSO for homegrown applications
- Separate identity systems from three acquisitions
- VPN with its own authentication
- Service accounts that bypass SSO entirely
- Security software have their own repository for identities
That’s not single sign-on. That’s 47 different identity silos pretending to be unified.
The SSO Promise vs. Reality
The Promise: “Implement SSO and users will have one identity, one password, seamless access to all applications.”
The Reality: Users have 5-7 different “single” sign-ons. They can’t remember which login works where. And your security team has zero unified visibility into who has access to what.
How We Got Here: The Five Deadly Sins
1. Application-First, Identity-Second
SSO was deployed to solve application access problems, not build identity infrastructure.
Each team chose their own solution:
- SaaS apps got Okta
- Microsoft shops deployed Azure AD
- AWS teams used IAM
- Custom apps got homegrown authentication
Nobody asked: “How do these systems talk to each other?”
The answer: They don’t.
2. Business Unit Autonomy
Different departments made independent decisions:
Sales: “We need Okta for our tools” IT: “We’re standardizing on Azure AD” Engineering: “We’re using AWS IAM” Finance: “Our ERP has its own identity system”
Each decision made sense locally. Together they created chaos.
3. Merger and Acquisition Identity Debt
Every acquisition brings a different SSO platform, unique user populations, and custom authentication methods. The path of least resistance: Keep both. Migrate “eventually.”
Eventually never comes. Now you have two Okta instances, three Azure AD tenants, and four Active Directory forests.
4. Legacy System Exclusion
SSO works for modern SaaS. But what about:
- Mainframe systems from the 1990s
- Custom applications without SAML support
- Database direct access
- Network equipment requiring local authentication
These systems maintain separate identity stores. Users need different credentials. “Single sign-on” stops being single.
5. The Service Account Blindspot
SSO works for humans. But service accounts, API keys, and automation credentials bypass SSO entirely. They’re managed in separate secret stores, configuration files, and spreadsheets.
Your SSO dashboard shows perfect compliance. Your actual identity landscape is chaos.
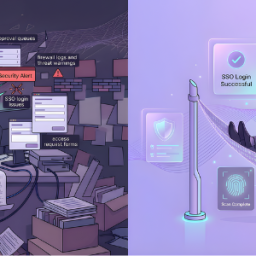
What You Built vs. What You Have
The Vision:
User → SSO → All Applications
The Reality:
User → Okta → Some SaaS Apps
User → Azure AD → Microsoft 365
User → Active Directory → Legacy Apps
User → AWS IAM → Cloud Infrastructure
User → VPN Login → Network Resources
User → Database Credentials → Direct Access
User → API Keys → Integrations
User → Local Credentials → Everything Else
You have SSO. You have nine of them. None talk to each other.
The Security Nightmare
No Unified Access View
Ask your security team: “Who has access to customer data?”
They’ll query Okta, Azure AD, AWS IAM, database grants, API keys, and Active Directory—then manually correlate results.
No Consistent Policy Enforcement
- Okta requires MFA
- Azure AD has conditional access
- AWS uses roles
- Legacy AD has group permissions
- Databases use local authentication
- APIs have no standard
Same user, seven different security standards. Attackers target the weakest link.
No Centralized Deprovisioning
When an employee leaves, deprovisioning triggers in the “main” system. But which system is main? What about accounts in the other six platforms? What about API keys they created?
Manual deprovisioning fails. Terminated employees retain access for months.
No Audit Trail Consolidation
Compliance requires: “Show me all access to this system over 90 days.”
Your audit trails are in Okta logs, Azure AD logs, AWS CloudTrail, application logs, database logs, and VPN logs. Correlating them requires manual effort or expensive SIEM implementations with coverage gaps.
The User Experience Disaster
Ask your users:
“How many different logins do you use?” Answer: 5-7
“Which login works where?” Response: “I try them all until one works”
“Has SSO made life easier?” Answer: “I still use a password manager for everything”
The “single” sign-on experience is anything but single.
The Cost of Fragmentation
License Costs: Multiple SSO platforms, redundant user seats, unused capacity
Operational Overhead: Teams managing each system, redundant workflows, manual reconciliation, help desk tickets
Security Risk: Orphaned accounts, inconsistent policies, delayed deprovisioning, visibility blind spots
Compliance Burden: Separate audits per system, manual evidence collection, inconsistent controls
You’re paying for “single” sign-on seven times while getting none of the promised benefits.
What Should Have Happened
SSO deployment should have started with identity strategy:
1. Single Source of Truth
Define ONE authoritative identity source. All users originate here. All other systems federate from this. Deprovisioning cascades everywhere.
2. Federated Architecture
Other SSO platforms become federation points, not identity sources:
- Azure AD federates from your source
- Okta federates from your source
- AWS IAM federates from your source
Users exist in one place. Authentication happens through federation.
3. Unified Governance Layer
Centralized policy management across all systems:
- Access requests go to one system
- Approvals follow consistent workflows
- Policies apply universally
- Audit trails consolidate centrally
4. Non-Human Identity Management
Treat service accounts and API keys as first-class identities with centralized secret management, automated rotation, and lifecycle governance.
The Path Forward
You can’t rip out 47 identity silos overnight. But you can stop making it worse:
Immediate Actions:
- Stop deploying new silos. Federate from existing systems instead.
- Inventory what you have. Count and document all identity systems.
- Identify the authoritative source. Pick one system as your foundation.
- Map federation relationships. Understand what can federate and what can’t.
- Establish governance. Implement a layer that enforces consistency.
Medium-Term Goals:
- Consolidate where possible. Reduce seven platforms to two or three.
- Federate extensively. What can’t consolidate should federate.
- Automate lifecycle. Provisioning/deprovisioning should cascade automatically.
- Implement unified reviews. Quarterly attestation across all systems.
- Centralize compliance. Aggregate logs for unified reporting.
The Leadership Conversation
“We implemented SSO to simplify identity. But tactical deployment created 47 different identity systems with security blind spots, increased costs, and frustrated users.”
The business impact:
- Security can’t answer “who has access to what”
- Terminated employees retain access in forgotten platforms
- Compliance requires manual effort across systems
- License costs are 3-4x what unified identity would cost
The ask:
- Designate one authoritative identity source
- Implement federation architecture
- Deploy unified governance layer
- Create 18-month consolidation roadmap
- Stop deploying new identity silos
The Bottom Line
Single Sign-On is a feature, not a strategy. When deployed without identity architecture, it creates fragmentation, complexity, and poor user experience.
Your 47 identity silos exist because SSO solved local application problems without considering enterprise architecture.
Every new SSO deployment without federation makes it worse. Every acquisition adds systems. Every business unit increases fragmentation.
The solution isn’t more SSO. It’s unified identity governance with SSO as one component.
The question: Will you fix this proactively—or wait until the next audit, breach, or compliance failure forces your hand?
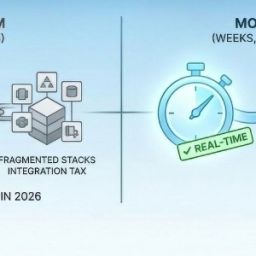
How Cross Identity Unifies Your Identity Chaos
Organizations drowning in identity fragmentation don’t need another SSO platform—they need identity orchestration that creates order above the chaos. Cross Identity was built for organisations operating multiple identity systems who need unified governance without infrastructure replacement.
Cross Identity transforms identity silos into unified architecture:
Single Source of Truth: Establish one authoritative identity repository while federating to all existing SSO platforms—Okta, Azure AD, AWS IAM, legacy systems—without forced migration.
Lifecycle Orchestration: When employees join, change roles, or leave, Cross Identity automatically provisions and deprovisions across all connected systems—eliminating orphaned accounts.
Unified Access Governance: Request access once, get permissions across all systems through intelligent orchestration. Conduct access reviews once, covering all silos simultaneously.
Complete Visibility: Finally answer “who has access to what” across all SSO platforms, cloud services, databases, and legacy systems through centralized analytics.
Federation Management: Connect disparate systems through automated federation configuration, turning silos into coordinated identity fabric.
Consolidated Compliance: Generate audit reports across all identity systems from one platform—what took weeks now takes minutes.
Organizations implementing Cross Identity reduce identity operational overhead by 60% and achieve unified visibility within 30 days—without replacing existing SSO infrastructure.
You don’t need to replace your identity investments. You need orchestration that makes them work together.
Schedule a Cross Identity assessment to discover how many identity silos you’re operating (it’s more than you think) and see how unified governance can deliver the SSO promise you never achieved—without replacing what you’ve deployed.
Source: Click Here