Every security conference, every vendor pitch, every board presentation now includes the magic words: “zero trust architecture.” Companies are spending millions on tools labeled “zero trust.” CISOs are checking the “zero trust strategy” box on their roadmaps.
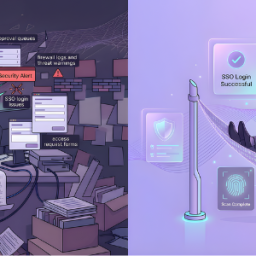
But here’s the uncomfortable truth: Most organizations haven’t implemented zero trust. They’ve just rebranded their existing perimeter security with more expensive tools.
The Zero Trust Theater
Zero trust has become cybersecurity’s most abused buzzword. The principle is sound: never trust, always verify. No implicit trust based on network location. Verify every access request, every time, based on identity, device, and context.
The reality in most enterprises? They’ve added MFA to their VPN, bought a CASB, deployed some endpoint agents, and called it “zero trust transformation.”
That’s not zero trust. That’s perimeter security with extra steps.
What Real Zero Trust Actually Requires
True zero trust architecture demands fundamental changes that make most organizations deeply uncomfortable:
1. Death of the Trusted Network Real zero trust means your internal network is treated as hostile as the internet. Every internal service requires authentication and authorization. Every connection is encrypted. Every request is verified.
Most companies can’t stomach this. Their legacy applications assume network-level trust. Their monitoring tools rely on unrestricted internal access. Their operational playbooks depend on “trusted zones.”
So they keep the trusted internal network and add a few verification layers around the edges. The perimeter didn’t disappear—it just became more expensive to maintain.
2. Identity as the Primary Security Perimeter In genuine zero trust, identity is the control plane. Not network segments. Not firewalls. Not VLANs.
This requires:
- Real-time identity verification for every access request
- Continuous authentication, not just login-time checks
- Granular, policy-based access to individual resources
- Dynamic trust scoring based on behavior and context
What most companies actually do: Add SSO, implement basic MFA, and continue making access decisions based on “are you on the corporate network?”
3. Micro-Segmentation at Application Level Zero trust means every application, every API, every resource enforces its own access policy. No lateral movement. No trust relationships between systems.
The reality: Companies implement some network micro-segmentation, but applications still trust anyone who reaches them from the internal network. The attack surface shrinks but doesn’t disappear.
4. Assume Breach Mentality True zero trust operates on the assumption that attackers are already inside. Every access is suspicious. Every request is validated. Every anomaly is investigated.
Most organizations still operate on a “keep the bad guys out” mentality. They’ve added detection tools, but their architecture still assumes that authenticated users are trustworthy.
The Rebranding Epidemic
Here’s how the “zero trust transformation” typically unfolds:
Phase 1: Vendor Engagement A vendor arrives with a “zero trust platform.” It’s actually their existing NAC, endpoint detection, or identity management tool with new marketing materials. The company buys it because it has “zero trust” in the name.
Phase 2: Perimeter Hardening The company strengthens their existing perimeter: better VPN, stricter firewall rules, enhanced MFA on external access. They call this “implementing zero trust principles.”
Phase 3: Checkbox Compliance They tick boxes: “Network segmentation? Check. MFA enabled? Check. Identity-aware proxy? Check.” Leadership sees checkmarks and declares success.
Phase 4: Unchanged Architecture Internal applications still trust network location. Service accounts still have standing privileges. Legacy systems still assume LAN = trusted. The fundamental architecture hasn’t changed—only the price tag.
Why Companies Can’t Admit the Truth
Security teams know they haven’t implemented real zero trust. But they can’t say it out loud. Here’s why:
Budget Already Spent Millions have been invested in “zero trust tools.” Admitting these don’t constitute zero trust architecture means admitting wasted spend.
Executive Expectations The board was promised zero trust transformation. The CISO presented a roadmap. Stakeholders expect to be “zero trust compliant.” Walking that back means losing credibility.
Operational Reality True zero trust requires re-architecting everything. Legacy applications need replacement or major refactoring. Workflows need redesign. Users need retraining. The organization isn’t ready for that level of disruption.
Vendor Complicity Vendors benefit from the ambiguity. They can sell perimeter security tools under the zero trust banner without forcing customers through painful transformation.
The Tell-Tale Signs of Zero Trust Theater
How do you know if your “zero trust strategy” is actually just expensive perimeter security?
Ask these questions:
- Can an attacker with stolen credentials move laterally through your internal network? If yes, you don’t have zero trust.
- Do your applications verify identity and authorization independently, or do they trust requests from the internal network? If the latter, you don’t have zero trust.
- If your VPN went down, would internal applications still enforce granular access controls? If no, you don’t have zero trust.
- Do you have service accounts with standing privileges and long-lived credentials? If yes, you don’t have zero trust.
- Can your monitoring tools see inside encrypted traffic between internal services? If no, you don’t have visibility for zero trust.
- Are access decisions made based on real-time risk assessment, or based on whether someone passed authentication once? If authentication-based, you don’t have zero trust.
What Actual Zero Trust Looks Like
A genuine zero trust implementation means:
Application-level enforcement: Every API, every microservice, every resource validates identity and authorization independently. Network location is irrelevant.
Identity-centric policies: Access decisions based on verified identity, device posture, behavioral analysis, and contextual risk—not network location.
No standing privileges: Just-in-time access provisioned for specific tasks with time-bound credentials. Service accounts eliminated or minimized.
Continuous verification: Authentication isn’t a one-time gate. Trust is continuously evaluated and can be revoked mid-session based on behavioral anomalies.
Encrypted everything: All traffic encrypted, even internal. Decryption and inspection happen at policy enforcement points, not perimeter devices.
Comprehensive logging: Every access attempt, every authorization decision, every anomaly logged and analyzed for threat detection.
This is painful, expensive, and operationally disruptive. Which is exactly why most companies haven’t done it.
The Path Forward: Honesty First
If your organization is on a “zero trust journey,” start with honesty:
Admit where you actually are. Don’t call perimeter improvements “zero trust implementation.” Call them what they are: strengthening existing defenses.
Set realistic timelines. True zero trust is a multi-year architectural transformation, not a product deployment. Communicate this to leadership.
Prioritize identity infrastructure. You can’t do zero trust without mature identity and access management. If your IAM is weak, start there before buying more tools.
Focus on greenfield first. Implement real zero trust for new applications and cloud workloads. Legacy systems can remain on enhanced perimeter security until they’re replaced.
Measure the right things. Stop measuring “zero trust adoption” by tools purchased. Measure it by: lateral movement prevention, privilege elimination, access granularity, and verification frequency.
The Bottom Line
Zero trust is a worthy goal. But slapping the label on perimeter security upgrades doesn’t make your organization more secure—it makes it more complacent.
Real zero trust requires admitting that your entire security architecture was built on flawed assumptions. It requires ripping out trust relationships, re-architecting applications, and fundamentally changing how your organization thinks about access.
Most companies aren’t ready for that conversation. So they buy “zero trust” tools, strengthen their perimeter, and declare victory.
Meanwhile, attackers who’ve already compromised credentials move laterally through “zero trust” networks as easily as they did through traditional ones.
The question isn’t whether zero trust is the right strategy. It is. The question is whether your organization is willing to do what zero trust actually requires—or whether you’re just buying expensive perimeter security in disguise.
At Cross Identity, we help organizations move beyond zero trust theater to build identity-centric security architectures that actually eliminate implicit trust. Because checking boxes isn’t the same as changing your attack surface.
Source: Click Here