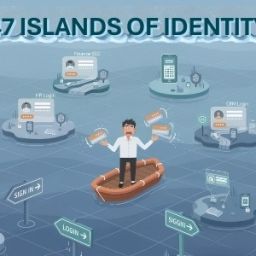
Identity is no longer just a “login” issue. It is the core of your security infrastructure. However, as teams scale, 12 critical gaps inevitably emerge, creating silent risks that standard tools miss.
The 12 Critical Identity Gaps-
- IT Framework & Cybersecurity Compliance: Modern regulations demand strict adherence to global IT frameworks. Failing to align your identity strategy with these mandates creates a baseline risk that can lead to heavy penalties and loss of trust.
- Orphan & Dormant Account Proliferation: Active access for former employees or unused system accounts act as “forgotten doors.” Without a unified view, these accounts sit unmonitored, waiting for an attacker to find them.
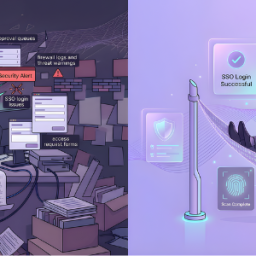
- Manual & Delayed Access Provisioning/Deprovisioning: Manual setups cause new hire productivity loss and leave systems dangerously exposed during delayed departures. If offboarding takes days instead of minutes, your perimeter is open.
- Excessive Entitlements & Access Creep: Users often accumulate privileges far beyond their current job requirements as they move through the company. This “access creep” creates a massive, unnecessary attack surface.
- Privileged Access Management Gaps: “Always-on” admin accounts for critical systems are a liability. Without converged governance, these high-value targets lack the temporary, just-in-time protections they require.
- Third-Party & Contractor Access Risks: External partners often access sensitive internal systems without the same rigorous controls as full-time staff, creating a “weak link” in your security chain.
Stop Building an “Identity Museum”
Most firms try to close these gaps by “stitching” together a dozen different tools. All this does is create a new gap: Complexity. You end up with an “Identity Museum,” a collection of expensive, disconnected tools that require months of custom coding to talk to each other. This “Integration Tax” drains your budget and leaves your security team managing APIs instead of managing risk.
With Cross Identity, it isn’t a collection of modules; it’s a single, unified codebase designed to move you from “exposed” to “secure” in just 9 weeks. Don’t settle for a stack that waits for a breach to tell you it’s broken.
Close the gaps. Consolidate your stack. Secure your future.