Enterprises don’t have a tooling problem. They have an infrastructure problem.
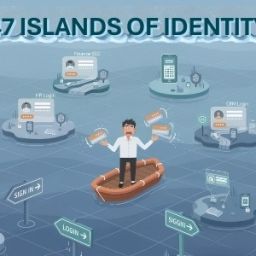
Cybersecurity has been built by stitching products together, SSO, MFA, IGA, PAM, CIEM, each operating with its own policies, risk logic, and response time. That model breaks in modern environments where identities are dynamic, access is continuous, and attacks move at machine speed.
Security assembled from disconnected tools cannot behave like infrastructure.
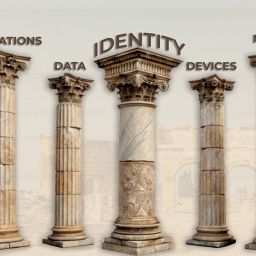
Why identity must be the foundation
Every action in the enterprise starts with identity, human, machine, workload, or API. Yet identity security is still fragmented across systems never designed to operate as one.
Cybersecurity-as-an-Infrastructure (CSaI) treats identity as the control plane. Access, privilege, governance, and risk operate from a single foundation, not separate products.
This enables:
- Consistent access decisions across all environments
- Instant policy and entitlement propagation
- Unified enforcement instead of integration lag
- Risk and trust, rebuilt for real time
Traditional models treat risk as something reviewed after access is granted. That’s too slow.
CSaI embeds risk into the infrastructure itself:
- Every access request is evaluated dynamically
- Behavior is continuously learned
- Anomalies trigger immediate adaptation
Trust is no longer binary. Privileges are just-in-time, sessions are continuously validated, and compliance becomes an always-on state.
Why this shift is inevitable
Identity volumes are exploding. Machine identities outnumber humans. AI-driven attacks exploit gaps in seconds. Stitched security stacks cannot keep up.
Cybersecurity must operate as infrastructure, continuous, contextual, and built into how the enterprise runs. CSaI is not an evolution of tools. It is a necessary architectural reset.