Pioneers in Converged IAM now bring to you the next generation of convergence.



Our Identity Security protects every digital identity, human or non-human, across every access point, in one unified system. By converging identity, access, and intelligence, and enabling business leaders to control, it stops breaches before they start and makes security seamless for everyone.
Pioneers in Converged IAM now bring to you the next generation of convergence.
Our Identity Security protects every digital identity, human or non-human, across every access point, in one unified system. By converging identity, access, and intelligence, and enabling business leaders to control, it stops breaches before they start and makes security seamless for everyone.
Pioneers in Converged IAM now bring to you the next generation of convergence.
Ranked by the world’s leading industry analysts, including KuppingerCole, our products are uniquely converged and futuristic.
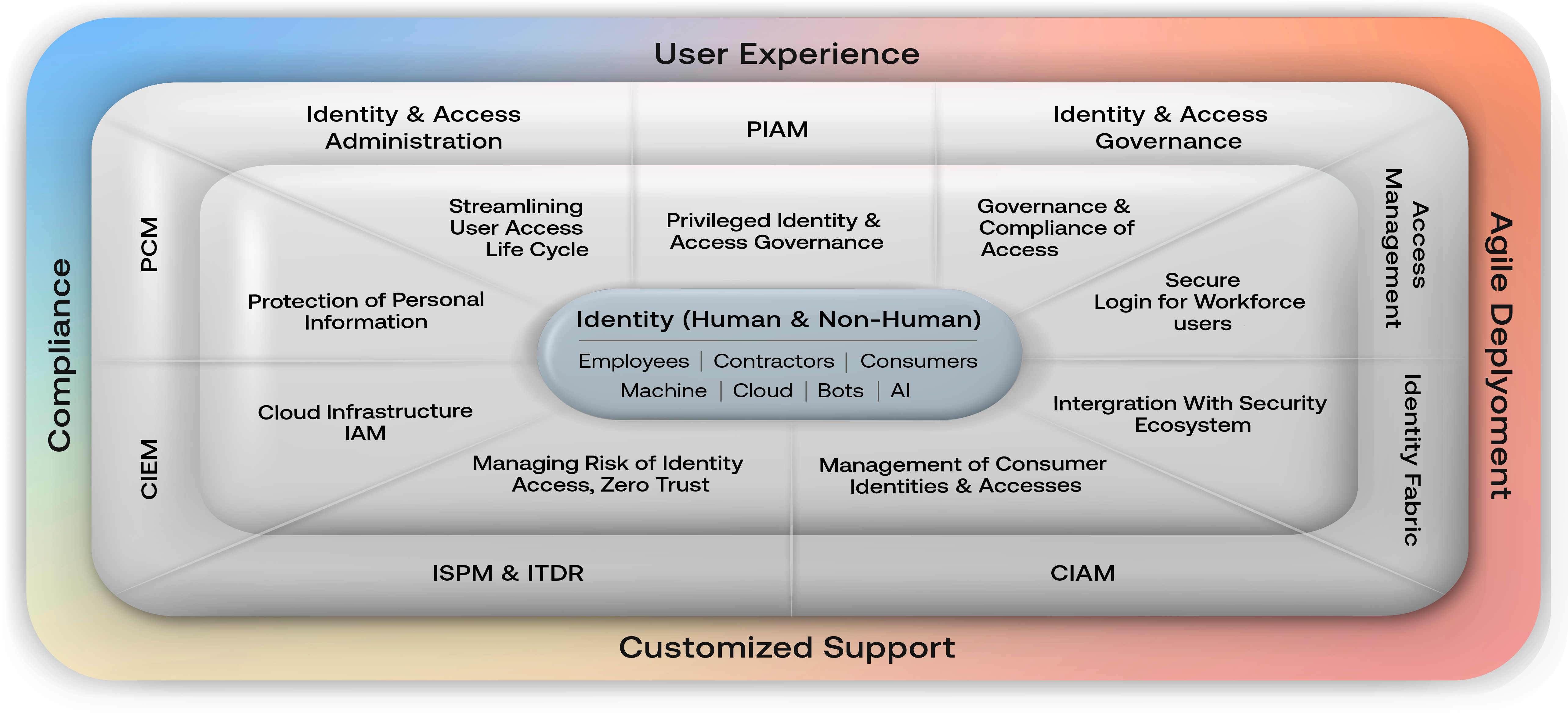
The Enterprise Family of products converges our world class enterprise IGA, with comprehensive Access Management, PIAM (Privileged Identity & Access Management), ISPM (Identity Security Posture Management) and ITDR (Identity Threat Detection and Response). This product range is designed for large customers that need a highly scalable identity security solution.
The MS Family of products offers you our simplified IAM, taking convergence to the next generation. It converges all types of identities, human and non-human. It contains a converged IAM platform with Workforce Access Management, Workforce IGA, Cloud Infrastructure & Entitlement Management (CIEM), Consumer Identity & Access Management (CIAM), Privileged Identity & Access Management (PIAM), Privacy Compliance Management (PCM), API Management and Identity Risk Management. This product range is designed for businesses who are looking for identity security that is simple and easy to deploy and use.
Identity Management and Identity Security are indispensable in the digital age. The concept of "Identity Fabrics" offers a comprehensive suite of Identity Services that enable seamless yet regulated access to services across the entire spectrum of users and devices. It represents a paradigm, not confined to a single technology, tool, or service, for structuring Identity and Access Management (IAM) within modern enterprises. While other vendors struggle to provide integration of access management, IGA, and PAM, Cross Identity already has a converged solution for these modules plus PIAM, CIEM, and Identity Risk Management. It also unifies human and non-human identities. Our Identity Fabric provides a distinctive dashboard offering unique visibility to all IAM related functions
The Enterprise Family of products converges our world class enterprise IGA, with comprehensive Access Management, PIAM (Privileged Identity & Access Management), IRM (IAM Risk Management comprising of ISPM (Identity Security Posture Management) and ITDR (Identity Threat Detection and Response)). This product range is designed for large customers that need a highly scalable identity security solution.
The MS Family of products offers you our simplified IAM, taking convergence to the next generation. It converges all types of identities, human and non-human. It contains a converged IAM platform with Workforce Access Management, Workforce IGA, Cloud Infrastructure & Entitlement Management (CIEM), Consumer Identity & Access Management (CIAM), Privileged Identity & Access Management (PIAM), Privacy Compliance Management (PCM), API Administration and Identity Risk Management. This product range is designed for businesses who are looking for identity security that is simple and easy to deploy and use.
The Enterprise Family of products converges our world class enterprise IGA, with comprehensive Access Management, PIAM (Privileged Identity & Access Management), ISPM (Identity Security Posture Management) and ITDR (Identity Threat Detection and Response). This product range is designed for large customers that need a highly scalable identity security solution.
The MS Family of products offers you our simplified IAM, taking convergence to the next generation. It converges all types of identities, human and non-human. It contains a converged IAM platform with Workforce Access Management, Workforce IGA, Cloud Infrastructure & Entitlement Management (CIEM), Consumer Identity & Access Management (CIAM), Privileged Identity & Access Management (PIAM), Privacy Compliance Management (PCM), API Management and Identity Risk Management. This product range is designed for businesses who are looking for identity security that is simple and easy to deploy and use.
Identity Management and Identity Security are indispensable in the digital age. The concept of “Identity Fabrics” offers a comprehensive suite of Identity Services that enable seamless yet regulated access to services across the entire spectrum of users and devices. It represents a paradigm, not confined to a single technology, tool, or service, for structuring Identity and Access Management (IAM) within modern enterprises. While other vendors struggle to provide integration of access management, IGA, and PAM, Cross Identity already has a converged solution for these modules plus PIAM, CIEM, and Identity Risk Management. It also unifies human and non-human identities. Our Identity Fabric provides a distinctive dashboard offering unique visibility to all IAM related functions.
Module | What It Does |
|---|---|
AM | Monitors access through SSO, MFA, password management, and adaptive policies for workforce and contractors |
IGA | Automate provisioning, deprovisioning, access reviews, and compliance |
CIAM | Manages secure, personalized logins and consent management for customers/consumers |
PIAM | Secures the riskiest users through Just-in-time access, session monitoring, least privilege enforcement, with identity administration and access governance. |
CIEM | Enables full visibility and control over cloud entitlements |
PCM | Manage data consent and meet global privacy requirements |
Identity Fabric | Unifying disparate IAM systems with common control |
ISPM & ITDR | Detect identity-based threats in real time, with automated response |
API | Process of designing, publishing, managing API connections—sharing them, controlling access, tracking their usage and enforcing security policies. |
Module | What It Does |
|---|---|
AM | Monitors access through SSO, MFA, password management, and adaptive policies for workforce and contractors |
IGA | Automate provisioning, deprovisioning, access reviews, and compliance |
CIAM | Manages secure, personalized logins and consent management for customers/consumers |
PIAM | Secures the riskiest users through Just-in-time access, session monitoring, least privilege enforcement, with identity administration and access governance |
CIEM | Enables full visibility and control over cloud entitlements |
PCM | Manage data consent and meet global privacy requirements |
Identity Fabric | Unifying disparate IAM systems with common control |
ISPM & ITDR | Detect identity-based threats in real time, with automated response |
API | Process of designing, publishing, managing API connections—sharing them, controlling access, tracking their usage and enforcing security policies |
Zero Trust has evolved from concept to business imperative, with leading analysts emphasizing converged IAM as the most effective foundation. Cross Identity's platform advantage becomes clear here: while others require stitching together disparate technologies, our unified Converged IAM Platform enables Zero Trust implementation from day one, achieving advanced CISA maturity levels in months rather than years


Zero Trust has evolved from concept to business imperative, with leading analysts emphasizing converged IAM as the most effective foundation. Cross Identity's platform advantage becomes clear here: while others require stitching together disparate technologies, our unified Converged IAM Platform enables Zero Trust implementation from day one, achieving advanced CISA maturity levels in months rather than years
IAM Risk Management (IRM) empowers organizations to detect, assess, and mitigate risks associated with user and privileged identities, entitlements, and access behaviors-across on-prem, cloud, and hybrid environments.
Cross Identity’s ISPM continuously detects access violations, risky behaviors, and entitlement drift across identities, apps, and permissions – all in one clean, actionable dashboard that helps you spot and address issues before they become security incidents.
Cross Identity’s ITDR analyzes signals from AM, IGA, PAM, CIEM, and security tools to spot account takeover, privilege abuse, anomalous access, and misconfigurations – then triggers policy-based responses in seconds to contain threats and keep your environment secure.
Capability | What It Does | Platform Module |
|---|---|---|
Access Management | Monitors access through SSO, MFA, password management, and adaptive policies for workforce and contractors | AM |
Identity Lifecycle & Governance | Automate provisioning, deprovisioning, access reviews, and compliance | IGA |
Customer IAM | Manages secure, personalized logins and consent management for customers/consumers | CIAM |
Privileged Access | Secures the riskiest users through Just-in-time access, session monitoring, least privilege enforcement, with identity administration and access governance. | PIAM |
Cloud User & Access Management | Enables full visibility and control over cloud entitlements | CIEM |
Privacy & Consent Management | Manage data consent and meet global privacy requirements | PCM |
Identity Fabric | Unifying disparate IAM systems with common control | Identity Fabric |
Threat Detection & Response | Detect identity-based threats in real time, with automated response | ISPM & ITDR |
API Management | Process of designing, publishing, managing API connections—sharing them, controlling access, tracking their usage and enforcing security policies. | API |
With decades of IAM expertise, Cross Identity delivers a platform that is…
Built on zero trust and modern security principles
Powerful yet affordable
Integrates with your stack, grows with your business
Stay aligned with mandates like GDPR, DPDPA, and HIPAA
With decades of IAM expertise, Cross Identity delivers a platform that’s:
Built on zero trust and modern security principles
Powerful yet affordable
Integrates with your stack, grows with your business
Stay aligned with mandates like GDPR, DPDPA, and HIPAA
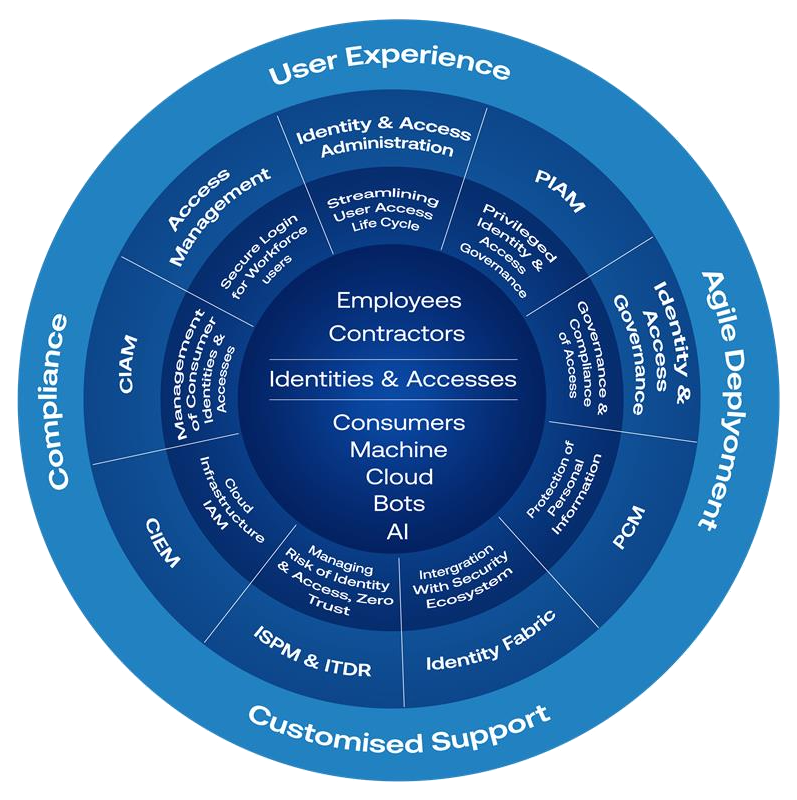
Access Management, Identity Governance, Privacy, Compliance, Infrastructure – all in one secure framework
It brings every identity — human, machine, consumer, workforce, and privileged — into a single secure model.
It brings every identity — human, machine, consumer, workforce, and privileged — into a single secure model.
It brings every identity — human, machine, consumer, workforce, and privileged — into a single secure model.
Identity Circle is the heart of our framework uniting Access Management, Identity Fabric, CIEM, PIAM and user experience into one simplified, secure architecture.
It brings every identity — human, machine, consumer, workforce, and privileged — into a single secure model.
We converge everything. From identity silos to a unified security fabric. From disconnected controls to coordinated governance. From complexity to clarity and control.
Gartner’s Converged IAM was a step in the right direction but limited in scope. We have taken it further – delivering a platform that unifies Access Management, Identity Governance, CIEM, and Risk into a single, integrated security architecture.
From startups to global enterprises, and from human to non-human identities — we cover it all, in one unified model. No matter the type of identity, we secure it
Cross Identity isn’t just about logging in. We secure the entire identity lifecycle — from onboarding to offboarding, and everything in between.
One platform brings together: Access Management, Identity Governance, Privacy, Compliance, Infrastructure – all in one secure framework.
CI adapts to your organization – from a startup to global team or scaling a multi-cloud enterprise
Our solution is built after years of real world IAM expertise, Cross Identity delivers a platform that’s:
Purpose built for today’s threat landscape
Scalable across teams without the enterprise price tag
Integrates with your existing stack and scales as you grow
Aligns with zero trust, privacy regulations and compliance mandates

We are the only fully converged identity security platform to receive leadership status across all five – according to one of the industry’s most respected analyst firms specializing in IAM.
Cross Identity is built on a foundation of original, in-house innovation — not acquisitions, not stitched-together tools. Our team holds four granted patents that power advanced capabilities across the platform, including:
What does this mean for your business

Cross Identity is built on a foundation of original, in-house innovation – not acquisitions, not stitched-together tools. Our team holds three granted patents that power advanced capabilities across the platform, including:

Let’s transform your identity strategy. Schedule a consultation and see how Cross Identity simplifies security, compliance, and control.
Interested in partnering with us?

Let’s transform your identity strategy.
Schedule a consultation and see how Cross Identity simplifies security, compliance, and control.
Interested in partnering with us?
Interested in partnering with us?
| Cookie | Duration | Description |
|---|---|---|
| cookielawinfo-checkbox-analytics | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Analytics". |
| cookielawinfo-checkbox-functional | 11 months | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Functional". |
| cookielawinfo-checkbox-necessary | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Necessary". |
| cookielawinfo-checkbox-others | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Other. |
| cookielawinfo-checkbox-performance | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Performance". |
| viewed_cookie_policy | 11 months | The cookie is set by the GDPR Cookie Consent plugin and is used to store whether or not user has consented to the use of cookies. It does not store any personal data. |
New: Free DPDPA Compliance Toolkit — 6 interactive tools to simplify your compliance journey →
