What is Identity & Access Risk Management?
IAM Risk Management (IRM) empowers organizations to detect, assess, and mitigate risks associated with user and privileged identities, entitlements, and access behaviors—across on-prem, cloud, and hybrid environments.
Why it matters:
- 80% of security breaches involve identity compromise
- Modern enterprises demand real-time risk visibility and continuous access assurance
- IRM is the foundation for Zero Trust maturity and regulatory compliance
Key Features
- Continuous Identity Risk Scoring: Real-time, contextual risk assessment for all user and non-human identities based on behavior, entitlements, device posture, and environment.
- Access Behavior Analytics: AI-driven analytics to detect abnormal sign-in, privilege escalation, lateral movement, or risky entitlement assignments.
- Automated Risk Remediation: Enforce policies (MFA, access revocation, step-up authentication, alerts) based on risk thresholds and policy rules.
- Privileged Access Risk Monitoring: Continuous oversight for privileged accounts, session monitoring, and rapid response to privilege misuse.
- Risk-aware Access Certification: Prioritized access reviews targeting high-risk identities and entitlements, reducing review fatigue.
- Comprehensive Risk Dashboards: Unified, real-time dashboards for CISOs and IAM admins to visualize organization-wide identity risks and trends.
- Regulatory Compliance: Built-in controls and evidence collection for PCI DSS, SOX, HIPAA, GDPR, RBI, and more.
How It Works
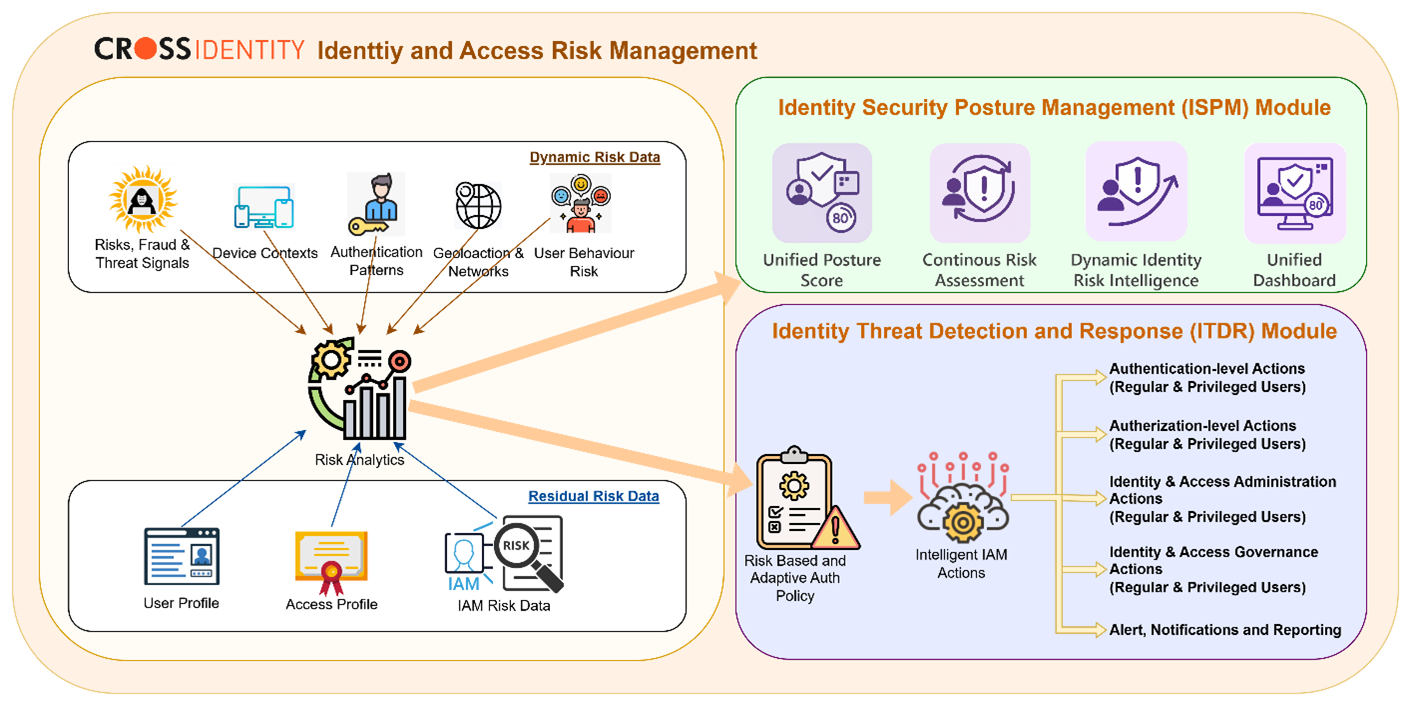
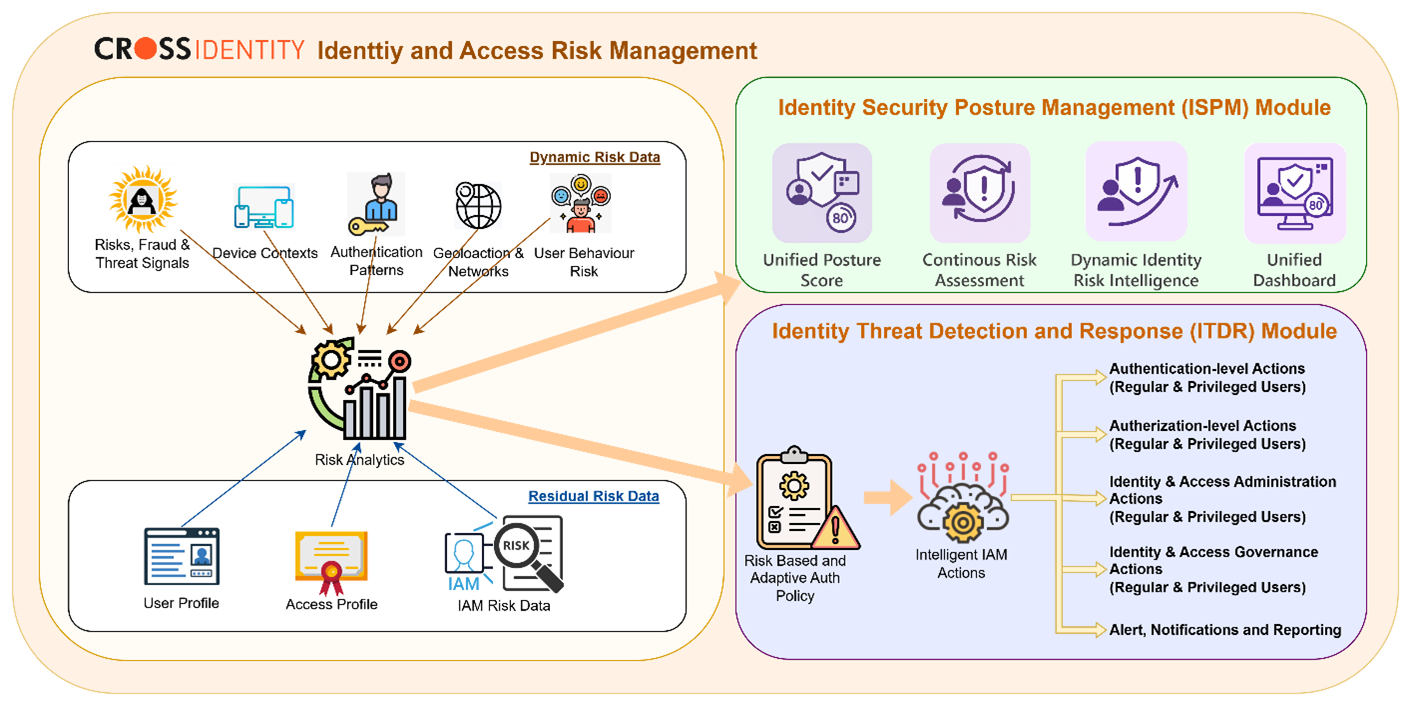
Risk analytics workflow: Dynamic & residual risk data feeds intelligent IAM actions.
(Source: Cross Identity)
Operational Flow
- Dynamic Risk Data Collection: Aggregates threat signals, device contexts, authentication patterns, network/geolocation, and user behavior risks.
- Risk Analytics: Correlates dynamic signals with user and access profiles for contextual scoring.
- Risk-Based Policy: Triggers intelligent IAM actions—authentication, authorization, admin/governance, alerting—based on risk posture.
- Residual Risk Data: Captures outcomes and updates IAM risk profiles for continuous improvement.
Integrations
- Native integration with Cross Identity AM, IGA, PAM, and CIEM modules
- Works with SIEM, SOAR, ITSM, and ZTNA solutions
- Supports 3rd-party risk feeds and custom connectors
Value Proposition
Proactive Threat Defense: Stop identity attacks before they escalate, using real-time risk signals.
Reduced Attack Surface: Identify and remove excessive entitlements, orphaned accounts, and risky access.
Audit-Ready Compliance: Simplify regulatory reporting and evidence collection with automated controls and dashboards.
Accelerate Zero Trust: Enable adaptive, risk-based access, aligned with CISA ZTMM and Zero Trust best practices.